
Axeploit
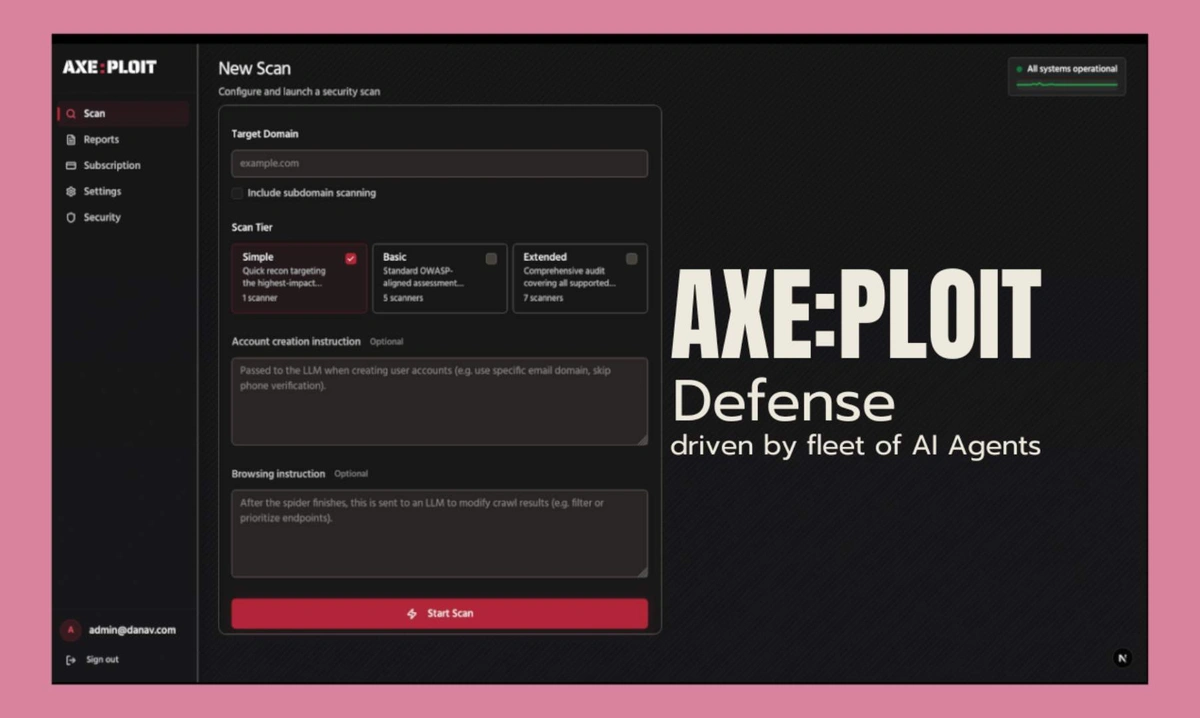
Axeploit signs up and navigates your platform independently, then scans for over 7,500 known vulnerabilities. Just like a real attacker.
The problem we kept running into with traditional dynamic scanners is the manual overhead required just to get them past the login screen. You usually have to feed them session tokens, record brittle login flows, or share user credentials. When the frontend changes, the flow breaks. Because of this, traditional tools often completely miss authentication-related flaws like email verification failures, mobile OTP bypasses, or weak tokens which make up a massive chunk of actual vulnerabilities.
We built Axeploit to operate autonomously, like a real user.
How it works:
Autonomous Auth: It registers its own accounts using real mobile numbers and email addresses, receives the OTPs.
Layout-Aware: The agent adapts in real-time without breaking the testing flow.
Deep Scanning: Once authenticated, it maps out the endpoints and scans for over 7,500 vulnerabilities.
Get in Touch
Interested in this opportunity? Contact the owner to explore details and potential collaboration.
Sign in to contact the listing owner
You May Also Like
aifeed
aifeed.dev
aifeed is a curated feed providing timely links to the latest news, tools, and developments in artificial intelligence and technology.
Talking Tree
talkingtree.app
Talking Tree is a 501(c)(3) nonprofit making enterprise-grade legal tech accessible for startups, small businesses, and nonprofits starting at $20/month. Developed by Fortune 500 attorneys
Tipstergpt
Tipstergpt.xyz
Get real-time football analytics and predictive insights with TipsterGPT. Discover trends, match stats, and strategy recommendations for every major league.